A single security breach can compromise confidential data, damage reputation, and lead to significant financial losses. Therefore, securing your Drupal website is crucial for ensuring the safety of your users and your business.
When it comes to security, Drupal has the best reputation. Because of its comprehensive security, many governments and global organizations that need truly secure websites choose Drupal. According to an annual report by a website security service Sucuri, in 2022, WordPress users accounted for 96.2% of infected websites, Joomla users for 1.9%, and Drupal users for just 0.6%.
However, like any other CMS, Drupal is not immune to security vulnerabilities, and it's up to the website owner to ensure that the website is secure. In this article, we will provide a comprehensive security checklist for Drupal websites to help you keep your website safe from potential security breaches.
Purpose of the Security Checklist

The security checklist provides a set of security best practices that you should follow to keep your Drupal website secure. These practices include disabling development modules, keeping your modules and Drupal core up to date, setting up strong administrator credentials, configuring SSL, and protecting against HTTP host header attacks. Following these security practices will help you minimize the risk of security breaches and ensure that your Drupal website is safe for your users.
Drupal Security Checklist

- Disable Development Modules: Devel modules should be disabled in the production environment to prevent any potential vulnerabilities.
- Deactivate any development settings that should not be used on the production (like TWIG auto-reload, etc.)
- Logging: Logs should be sent to syslog instead of DBlog (if applicable) to ensure that they are secure and not overwhelming the DB capacity with some potential attacker’s actions.
- Module Updates: Modules with security fix releases should be updated to the latest version to prevent any known vulnerabilities.
- Drupal Core Updates: Drupal Core should be kept up to date to ensure that the website is protected against any known security issues.
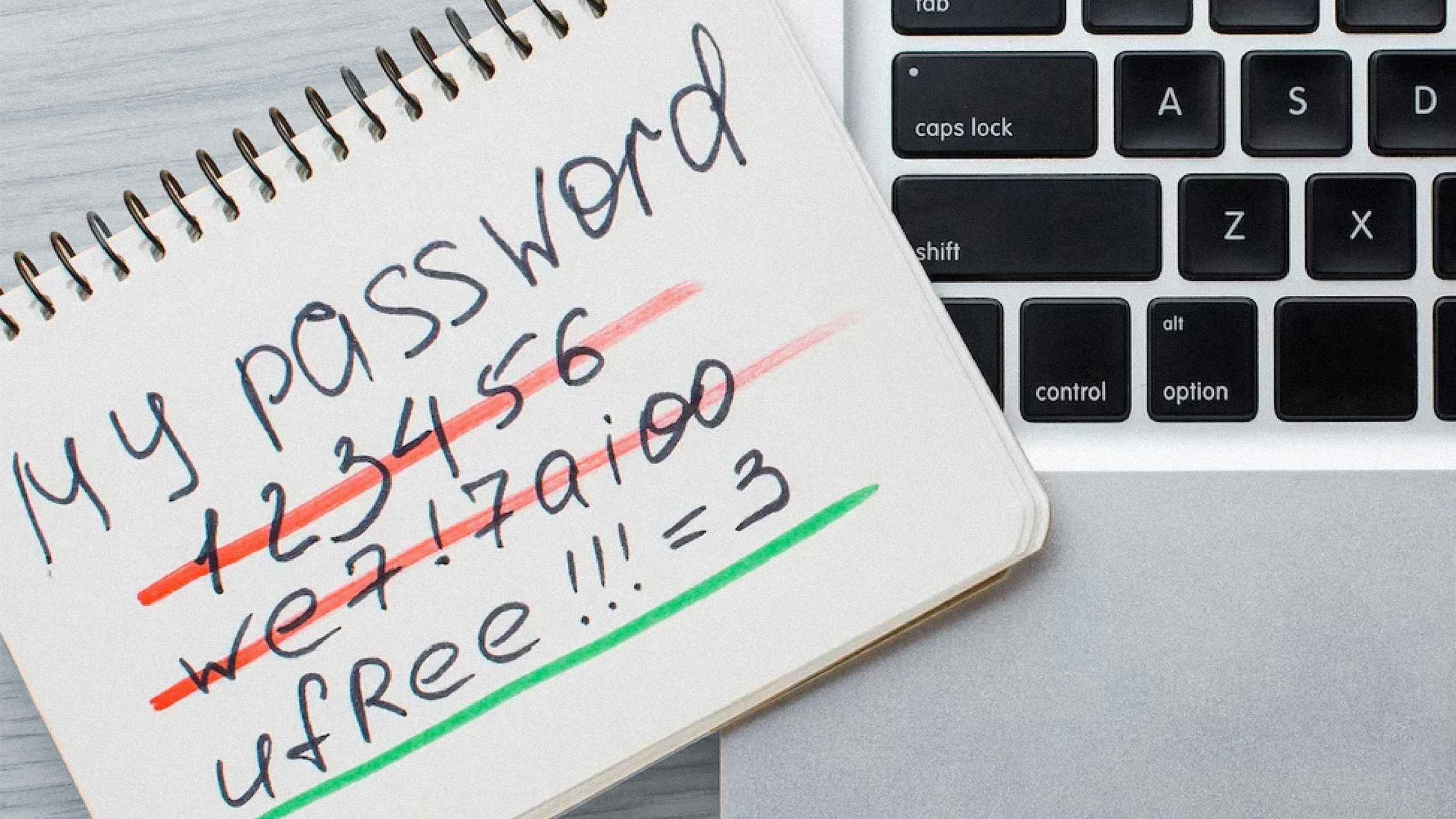
- Strong Administrator Password: The administrator password should be strong enough to prevent any unauthorized access.
- Strong Administrator Username: The default administrator's username should also be strong enough to prevent any unauthorized access.
- Remove SQL Dumps: All SQL dumps should be removed from the production server to prevent any potential data breaches.
- File Permissions: Set up the correct file and directory tree permissions as per Drupal's best practices to protect sensitive files and directories.
- Disable User Registration: If necessary, user registration should be disabled to prevent any unauthorized access to the website.
- Captcha: Public forms should have a captcha enabled to prevent any automated attacks.
- SSL Configuration: The website should be configured with SSL to encrypt communication between the server and the client.
- HTTP HOST Header Protection: The website should be protected against HTTP HOST header attacks to prevent any potential vulnerabilities.
- Private Folder Setup: It is important to set up a private folder to protect sensitive files and directories.
- Non-Blocking Issues: Any non-blocking issues from DBlog should be recorded in the respective task in the backlog to address them later.
- Security Headers: Make sure that security headers are set to protect the website against any potential vulnerabilities.
Wrapping Up

Securing your Drupal website is essential for protecting your users' data and your business reputation. Following the security best practices outlined in this article will help you keep your Drupal website secure from potential security breaches. If you need help securing your Drupal website, you can always contact a professional Drupal development agency like Five Jars for assistance.
Check out additional resources to use in your team: